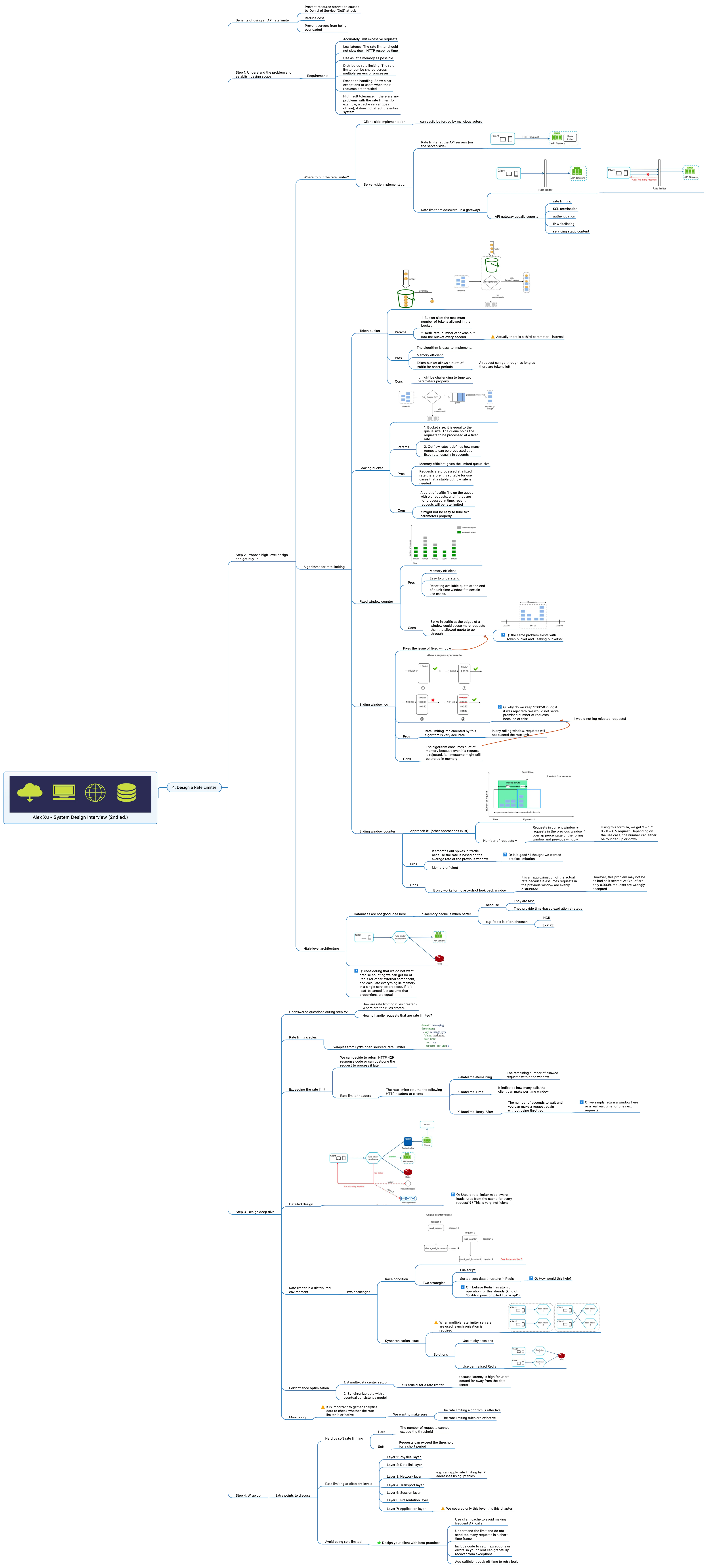
System Design Interview - Chapter 4 - Design a Rate Limiter

Every popular software should have a Rate Limiter. It prevents DDOS attack, reduces cost and prevents servers from being overloaded.
There are some tricky questions to be considered during implementation of Rate Limiter:
- Where to put Rate Limiter: client-side, server-side, gateway?
- Algorithms for rate limiting. There are many algorithms with pros and cons: Token bucket, Leaking bucket, Fixed window counter, Sliding window log, Sliding window counter. Your business needs will define the right algorithm.
- How are rate limiting rules created?
- Where are the rules stored?
- How to handle requests that are rate limited?
These questions are disclosed in a very interesting Chapter 4 of the book:
HIGHLY RECOMMEND!
Sharing my mind map with all the details as usual:
See also:
- System Design Interview - Chapter 3 - A Framework for System Design Interviews
- System Design Interview - Chapter 2 - Back-to-the-envelope estimation
- System Design Interview - Chapter 1 - Scale from zero to millions of users
- System Design Interview - Chapter 8 - Design a URL Shortener
- System Design Interview - Chapter 7 - Design a Unique ID Generator in Distributed Systems